Hackers backed by a powerful nation-state have been exploiting two zero-day vulnerabilities in Cisco firewalls in a five-month-long campaign that breaks into government networks around the world, researchers reported Wednesday.
The attacks against Cisco’s Adaptive Security Appliances firewalls are the latest in a rash of network compromises that target firewalls, VPNs, and network-perimeter devices, which are designed to provide a moated gate of sorts that keeps remote hackers out. Over the past 18 months, threat actors—mainly backed by the Chinese government—have turned this security paradigm on its head in attacks that exploit previously unknown vulnerabilities in security appliances from the likes of Ivanti, Atlassian, Citrix, and Progress. These devices are ideal targets because they sit at the edge of a network, provide a direct pipeline to its most sensitive resources, and interact with virtually all incoming communications.
Cisco ASA likely one of several targets
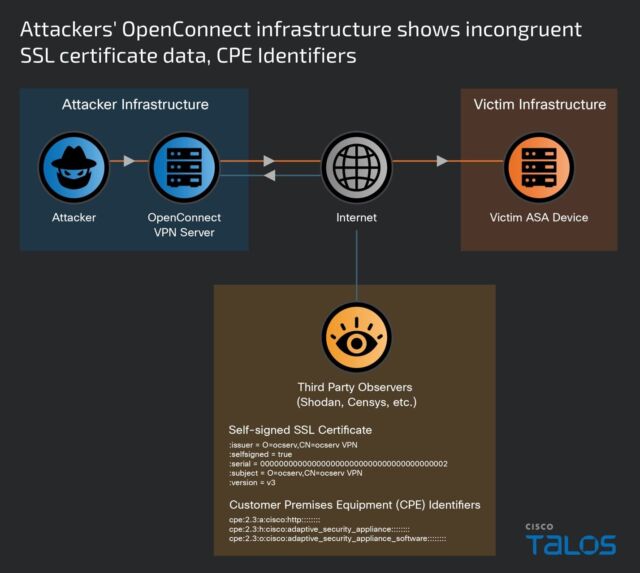
On Wednesday, it was Cisco’s turn to warn that its ASA products have received such treatment. Since November, a previously unknown actor tracked as UAT4356 by Cisco and STORM-1849 by Microsoft has been exploiting two zero-days in attacks that go on to install two pieces of never-before-seen malware, researchers with Cisco’s Talos security team said. Notable traits in the attacks include:
- An advanced exploit chain that targeted multiple vulnerabilities, at least two of which were zero-days
- Two mature, full-feature backdoors that have never been seen before, one of which resided solely in memory to prevent detection
- Meticulous attention to hiding footprints by wiping any artifacts the backdoors may leave behind. In many cases, the wiping was customized based on characteristics of a specific target.
Those characteristics, combined with a small cast of selected targets all in government, have led Talos to assess that the attacks are the work of government-backed hackers motivated by espionage objectives.
“Our attribution assessment is based on the victimology, the significant level of tradecraft employed in terms of capability development and anti-forensic measures, and the identification and subsequent chaining together of 0-day vulnerabilities,” Talos researchers wrote. “For these reasons, we assess with high confidence that these actions were performed by a state-sponsored actor.”
The researchers also warned that the hacking campaign is likely targeting other devices besides the ASA. Notably, the researchers said they still don’t know how UAT4356 gained initial access, meaning the ASA vulnerabilities could be exploited only after one or more other currently unknown vulnerabilities—likely in network wares from Microsoft and others—were exploited.
“Regardless of your network equipment provider, now is the time to ensure that the devices are properly patched, logging to a central, secure location, and configured to have strong, multi-factor authentication (MFA),” the researchers wrote. Cisco has released security updates that patch the vulnerabilities and is urging all ASA users to install them promptly.
UAT4356 started work on the campaign no later than last July when it was developing and testing the exploits. By November, the threat group first set up the dedicated server infrastructure for the attacks, which began in earnest in January. The following image details the timeline:
Cisco
One of the vulnerabilities, tracked as CVE-2024-20359, resides in a now-retired capability allowing for the preloading of VPN clients and plug-ins in ASA. It stems from improper validation of files when they’re read from the flash memory of a vulnerable device and allows for remote code execution with root system privileges when exploited. UAT4356 is exploiting it to backdoors Cisco tracks under the names Line Dancer and Line Runner. In at least one case, the threat actor is installing the backdoors by exploiting CVE-2024-20353, a separate ASA vulnerability with a severity rating of 8.6 out of a possible 10.